Cybersecurity risk management is a systematic approach to identifying, analyzing, and mitigating security threats that could compromise your organization’s data, systems, and operations. It works by continuously evaluating your attack surface, implementing security controls, and monitoring for new vulnerabilities that emerge as your technology environment evolves.
The practice provides quantifiable benefits: reduced financial losses from data breaches, lower cybersecurity insurance premiums, and compliance with regulatory requirements like NIST 800-53 Controls and ISO 27001. Organizations use cybersecurity risk management to prioritize security investments, allocate resources to high-impact vulnerabilities, and build incident response capabilities that minimize downtime during cyber attacks.
A complete cyber risk management strategy consists of four core components: asset identification, risk analysis and evaluation, risk treatment through security controls, and continuous monitoring. These elements work together to create a defense strategy that adapts to new threats while protecting business operations.
With evolving attack surfaces and rising threats, having a reliable cybersecurity risk management solution is more important than ever to keep businesses safe and resilient.
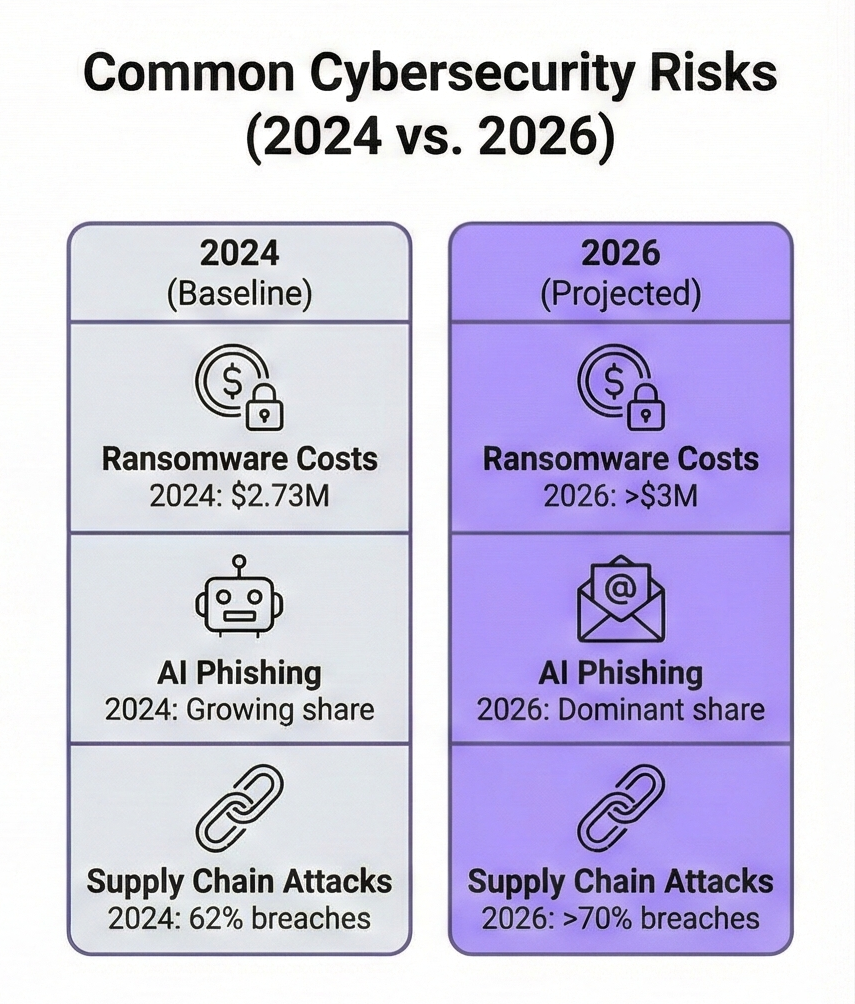
The attack surface for most organizations has expanded by 300% over the past five years, driven by cloud migrations, remote work adoption, and increased API usage. Ransomware attacks cost businesses $20 billion in 2024, with average recovery costs exceeding $1.85 million per incident. Supply chain vulnerabilities now account for 62% of successful breaches, making third-party risk management a requirement rather than an option.
Your organization faces threats that barely existed three years ago. AI-generated phishing now makes up a large share of attacks and achieves significantly higher click and compromise rates than traditional email scams, making it far harder for employees to spot malicious messages. Cloud misconfigurations and exposed secrets are now a leading cause of data exposure, with many cloud environments running publicly reachable workloads or storage that contain sensitive data. Meanwhile, modern DDoS campaigns can degrade or take down critical services within minutes if you lack layered monitoring and mitigation controls, directly impacting revenue and operations.
What is Cybersecurity Risk Management?
Cybersecurity risk management is the process of identifying, assessing, and controlling threats to your organization’s digital assets, information systems, and data. It combines technical security measures with business risk assessment to protect against cyber attacks while maintaining operational efficiency.
The practice differs from general IT risk management because it focuses specifically on security threats: malware, unauthorized access, data breaches, insider threats, and system compromises. You evaluate each risk based on likelihood and potential impact, then implement controls proportional to the threat level.
Effective cyber risk management requires understanding your risk appetite—the amount of security risk you’re willing to accept to achieve business objectives. A financial services company has lower risk tolerance than a retail business because regulatory requirements and customer expectations demand stricter data protection.
The discipline incorporates threat intelligence to stay current with emerging attack methods. You monitor dark web activity, track vulnerability disclosures, and analyze threat actor tactics to predict where attacks might occur before they happen.
The Importance of Cyber Risk Management
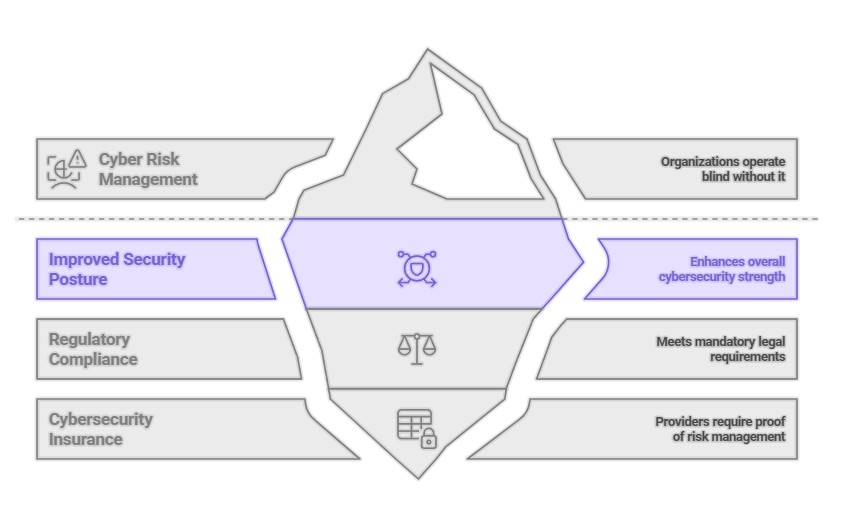
Organizations without structured cyber risk management operate blind to their vulnerabilities. You can’t protect what you don’t know exists, and you can’t prioritize defenses without understanding which assets matter most to your business.
Improved Security Posture
Your security posture represents your overall cybersecurity strength across people, processes, and technology. Cyber risk management improves this posture by identifying gaps in your defenses and implementing controls that address the highest-priority vulnerabilities first.
You gain visibility into your entire attack surface through vulnerability assessment and penetration testing. These activities reveal weaknesses in network configurations, application code, access controls, and endpoint security before attackers exploit them.
Organizations with mature risk management programs detect breaches 54% faster than those without structured processes. Faster detection means less time for attackers to move laterally through your network, steal data, or deploy ransomware. The average dwell time for undetected breaches is 207 days—cyber risk management reduces this to weeks or days.
Regulatory Compliance
Meeting regulatory compliance requirements is mandatory for organizations in healthcare, finance, government contracting, and payment processing. Cyber risk management frameworks align with regulations like HIPAA, SOX, GDPR, and PCI-DSS, ensuring you implement required security controls.
Non-compliance carries substantial penalties. GDPR violations can reach the greater of €20 million or 4% of annual global turnover. For multinational enterprises, the percentage-based fine is almost always the higher figure, representing a catastrophic financial risk. PCI-DSS non-compliance results in fines up to $500,000 per month plus increased payment processing fees. Beyond financial penalties, you face reputational damage that drives customers to competitors.
Risk assessments document your compliance efforts, providing auditors with evidence that you’ve identified risks and implemented appropriate controls. This documentation proves you’re making good-faith efforts to protect sensitive information, which can reduce penalties if a breach occurs.
Cybersecurity Insurance
Cybersecurity insurance providers now require proof of active risk management before issuing policies. You must demonstrate vulnerability management programs, incident response plans, endpoint detection response capabilities, and employee security awareness training.
Premiums decrease when you implement strong security controls. Organizations with mature risk management programs pay 20-30% less than those with basic security measures. Insurers calculate premiums based on your likelihood of filing a claim, and effective risk management directly reduces that probability.
Coverage limits increase when you can prove your security posture meets industry standards. Without documented risk assessments and control implementations, insurers cap coverage at lower amounts or exclude specific attack types like ransomware from your policy.
Cybersecurity Risk Management Process Explained
The risk management process follows a continuous cycle that repeats as your environment changes. You can’t complete risk management once and consider it finished—new vulnerabilities emerge daily, and your attack surface shifts as you adopt new technologies.
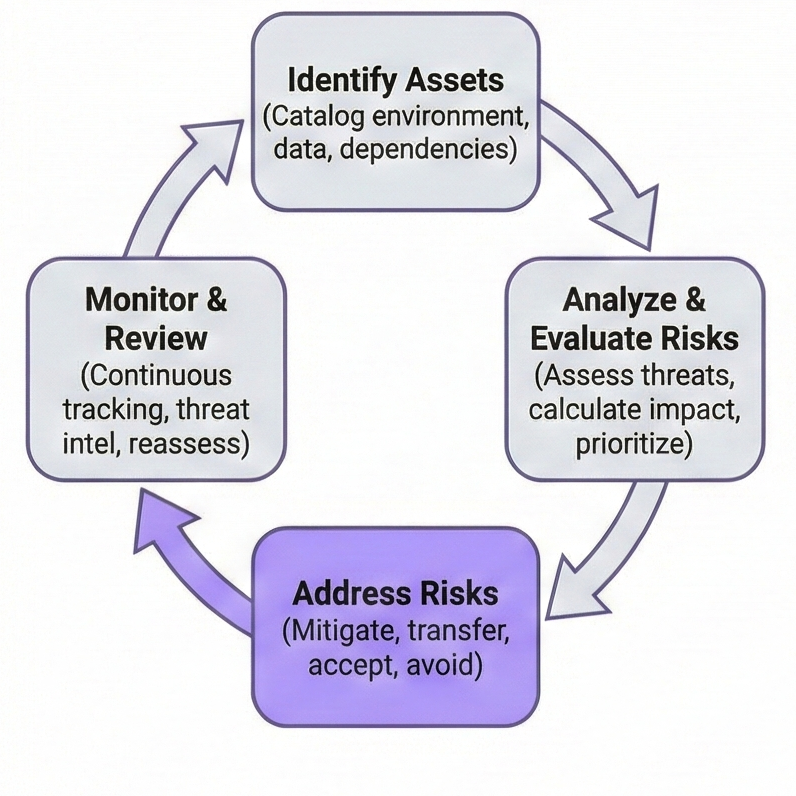
1. Identifying Assets
Asset identification catalogs everything in your environment: servers, databases, and network devices, as well as ephemeral cloud resources (containers/serverless functions), Shadow IT, and exposed API endpoints. In a modern environment, these “invisible” assets are often the primary entry points for attackers.
Physical assets include on-premises servers, networking equipment, and employee devices. Digital assets encompass software applications, cloud services, APIs, and data stores. Information assets cover customer records, intellectual property, financial data, and employee information.
Classification assigns value to each asset based on confidentiality, integrity, and availability requirements. Customer payment data requires high confidentiality and integrity, while public marketing materials need high availability but low confidentiality protection.
You map dependencies between assets to understand how compromising one system affects others. A database breach might expose customer data directly, but it could also provide credentials to access additional systems, multiplying the damage.
2. Analyzing and Evaluating Risks
Risk analysis examines each identified asset to determine what could go wrong, how likely each scenario is, and what impact a successful attack would cause. You combine threat intelligence with vulnerability data to calculate risk scores for each asset.
Qualitative risk analysis uses categories like low, medium, and high to rank risks. This approach works well for initial assessments when you lack detailed data about threat probabilities or financial impacts.
Quantitative risk analysis assigns dollar values to potential losses using the FAIR (Factor Analysis of Information Risk) taxonomy. You calculate Annual Loss Expectancy (ALE) by multiplying Single Loss Expectancy (SLE) by the Annual Rate of Occurrence (ARO). This allows the board to view cyber risk as a standard financial line item. If a database breach costs $2 million and occurs once every five years, your ALE is $400,000.
Vulnerability assessments scan your environment for known weaknesses: unpatched software, misconfigured systems, weak passwords, and exposed services. Automated scanners identify thousands of potential issues, which you then prioritize based on exploitability and asset value.
Threat modeling examines how attackers might compromise your systems. You map potential attack paths from initial access through privilege escalation to data exfiltration, identifying which controls would break the attack chain at each stage.
3. Addressing Risks
Risk treatment selects appropriate responses for each identified risk: avoid, transfer, mitigate, or accept. You choose treatments based on risk severity, implementation costs, and business impact.
Risk avoidance eliminates the risk entirely by removing the vulnerable asset or discontinuing the risky activity. If a legacy application has unfixable vulnerabilities and minimal business value, you retire it rather than trying to secure it.
Risk transfer shifts the financial burden to another party through cybersecurity insurance or contractual indemnification with third-party vendors. By ensuring service-level agreements (SLAs) include security liability, you protect the organization from losses caused by a partner’s breach.
Risk mitigation implements security controls that reduce likelihood or impact. Firewalls, encryption, access controls, intrusion detection systems, and security awareness training all mitigate specific risks without eliminating them completely.
Risk acceptance acknowledges some risks aren’t worth addressing. If mitigating a risk costs $100,000 but the potential loss is $10,000, you document the decision to accept the risk and move resources to higher-priority issues.
4. Monitoring and Review
Continuous monitoring tracks security events in real-time, detecting anomalies that indicate potential attacks. Security Information and Event Management (SIEM) systems aggregate logs from across your environment, correlating events to identify suspicious patterns.
Behavioral anomaly detection establishes baselines for normal activity, then alerts when deviations occur. An employee who typically accesses 50 files per day suddenly downloading 5,000 files triggers investigation for potential data theft.
Periodic reviews reassess risks as your environment evolves. You update risk registers quarterly or when significant changes occur: new applications, cloud migrations, organizational restructuring, or regulatory updates.
Threat intelligence feeds provide information about new vulnerabilities, attack techniques, and threat actor campaigns. You incorporate this intelligence into your risk assessments, adjusting controls to address emerging threats before they affect your organization.
8 Benefits of a Robust Cybersecurity Risk Management Strategy
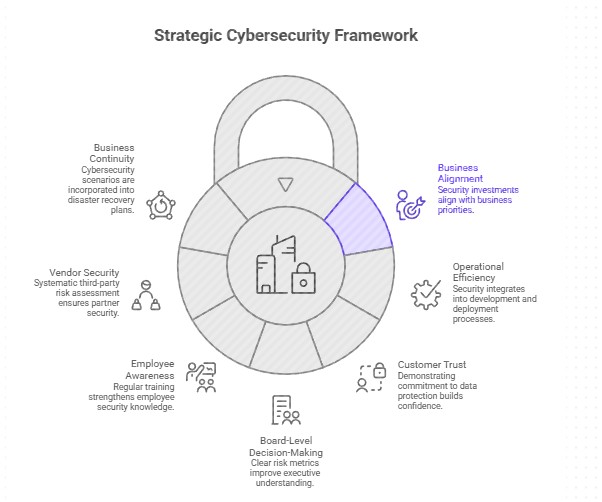
A mature cyber risk management strategy delivers measurable improvements in security outcomes, cost efficiency, and business resilience. Organizations with documented risk management programs experience 50% fewer successful breaches and recover from incidents 60% faster than those without structured approaches.
The latest research shows the average global cost of a data breach has climbed to around USD 4.9 million, reflecting double‑digit growth in just a year. Organizations that have a dedicated incident response team and regularly test their incident response plans cut those costs dramatically, with studies showing savings in the range of USD 1.5–2.7 million per breach compared to peers that do not. That is real money protected on every major incident, not just an abstract risk metric.
1. Financial impact of attacks is reduced through early detection and rapid response, with dedicated incident response teams saving millions per breach compared to unprepared peers.
2. Security investments align with business priorities. You allocate budget to protect high-value assets rather than spreading resources evenly across all systems.
3. Operational efficiency improves when security integrates into development and deployment processes. Secure coding practices prevent vulnerabilities before they reach production.
4. Customer trust increases when you demonstrate commitment to data protection. Published security certifications, completed compliance audits, and transparent incident disclosure build confidence that you handle customer information responsibly.
5. Board-level decision-making improves with clear risk metrics. Executives understand security posture in business terms: percentage of critical assets protected, mean time to detect threats, and residual risk levels after control implementation.
6. Employee security awareness strengthens through regular training tied to your risk assessment findings. You educate staff about specific threats relevant to their roles: finance teams learn about business email compromise, while developers study secure coding practices.
7. Vendor and supply chain security improves through systematic third-party risk assessment. You require security questionnaires, audit reports, and contractual security obligations before sharing data with partners or service providers.
8. Business continuity planning incorporates cybersecurity scenarios, ensuring your organization can maintain operations during and after cyber attacks. Disaster recovery plans address ransomware, DDoS attacks, and data corruption with tested procedures for rapid restoration.
Common Cybersecurity Risks Businesses Face Today
Ransomware attacks encrypt business-critical data and demand payment for decryption keys. Attackers target backups first to eliminate recovery options, forcing organizations to pay or lose data permanently. The average ransom demand reached $2.73 million in 2024, with only 57% of victims who pay receiving functional decryption tools.
Phishing campaigns trick employees into revealing credentials or installing malware. Modern attacks use AI to craft convincing emails that bypass traditional spam filters. Spear phishing targets specific individuals with personalized messages referencing real business activities or relationships.
Supply chain attacks compromise software vendors or service providers to gain access to their customers. The SolarWinds breach affected 18,000 organizations through a single compromised software update. You inherit risks from every third party that accesses your data or systems.
Cloud misconfigurations expose data through publicly accessible storage buckets, overly permissive access controls, or disabled security features. Automated scanners constantly search for misconfigured cloud resources, and attackers exploit discovered vulnerabilities within hours.
Insider threats come from employees, contractors, or business partners who abuse legitimate access. Malicious insiders steal intellectual property, sabotage systems, or sell customer data. Negligent insiders accidentally expose data through poor security practices or falling for social engineering.
API vulnerabilities allow unauthorized access to backend systems and databases. APIs often lack proper authentication, rate limiting, or input validation, enabling attackers to extract large datasets or manipulate business logic.
DDoS attacks overwhelm network infrastructure with traffic. Modern hyper-volumetric attacks regularly exceed 2–5 Tbps in size or 200 million requests per second (rps). By 2026, attackers are increasingly using AI to vary traffic patterns in real-time, making them capable of knocking even large, cloud-native organizations offline.
Cyber Risk Management Frameworks
Frameworks provide structured methodologies for implementing cyber risk management. You select frameworks based on industry requirements, regulatory obligations, and organizational maturity.
NIST CSF
The NIST Cybersecurity Framework (CSF) 2.0 organizes security activities into six functions: Govern, Identify, Protect, Detect, Respond, and Recover. This addition of “Govern” emphasizes that cybersecurity is a corporate leadership responsibility, not just a technical one. This framework works for organizations of all sizes and industries because it focuses on outcomes rather than prescribing specific technologies.
You use NIST CSF to assess current security posture, identify gaps, and prioritize improvements. The framework defines three implementation tiers—Partial, Risk Informed, and Adaptive—that describe maturity levels for each security function.

NIST 800-53 Controls
NIST 800-53 provides a catalog of 1,000+ security controls for federal information systems. Controls cover 20 families including access control, incident response, system and communications protection, and supply chain risk management.
You select controls based on system categorization: Low, Moderate, or High impact. High-impact systems require the most extensive controls because their compromise would cause severe damage to organizational operations, assets, or individuals.
NIST 800-171 Controls
NIST 800-171 specifies 110 security requirements for protecting Controlled Unclassified Information (CUI) in non-federal systems. Defense contractors and federal grant recipients must implement these controls to handle government data.
Requirements cover 14 families including audit and accountability, configuration management, identification and authentication, and physical protection. You document implementation status for each requirement and create Plans of Action and Milestones (POA&Ms) for any gaps.
ISO 27001
ISO 27001 establishes requirements for Information Security Management Systems (ISMS). Certification requires implementing appropriate controls from Annex A, conducting regular audits, and continuously improving security processes.
The standard requires risk assessment to select applicable controls rather than implementing all 93 Annex A controls. You document your risk treatment decisions in a Statement of Applicability that explains which controls you’ve implemented and why you excluded others.
ISO 27002
ISO 27002 provides implementation guidance for ISO 27001 controls. It details specific security practices for each control area: organizational controls, people controls, physical controls, and technological controls.
You reference ISO 27002 when implementing ISO 27001 to understand best practices for each required control. The guidance includes considerations for cloud computing, mobile devices, and emerging technologies.
PCI-DSS
The Payment Card Industry Data Security Standard (PCI-DSS) protects cardholder data for organizations that process credit card payments. Requirements include network segmentation, encryption, access controls, vulnerability management, and regular security testing.
Compliance level depends on transaction volume: Level 1 merchants processing over 6 million transactions annually require annual onsite audits, while smaller merchants complete self-assessment questionnaires. Non-compliance results in fines and potential loss of payment processing privileges.
Center for Internet Security (CIS) Controls
CIS Controls define 18 prioritized security actions that block the most common attack patterns. Implementation Groups organize controls by organizational size and sophistication: IG1 for small organizations with limited resources, IG2 for medium organizations, and IG3 for enterprises with advanced capabilities.
You start with basic cyber hygiene controls like inventory of assets, data protection, and account management before progressing to advanced controls like penetration testing and security awareness training.
DoD RMF
The Department of Defense Risk Management Framework (RMF) provides a six-step process for securing defense systems: Categorize, Select, Implement, Assess, Authorize, and Monitor. The framework ensures consistent security practices across all DoD components and contractors.
Authorization decisions weigh security risks against mission requirements. Authorizing officials accept residual risks based on implemented controls, threat environment, and mission criticality.
FAIR Framework
Factor Analysis of Information Risk (FAIR) quantifies cyber risk in financial terms. You model loss scenarios by estimating threat event frequency and probable loss magnitude, producing risk estimates in dollars rather than qualitative ratings.
FAIR analysis supports cost-benefit decisions for security investments. You compare the cost of security controls against the expected risk reduction they provide, investing in controls that deliver positive return on security investment.
Developing Your Cyber Risk Management Strategy: Tips for Success
Strategy development requires executive sponsorship, adequate resources, and commitment to continuous improvement. You can’t bolt risk management onto existing processes—it must integrate into how your organization makes technology and business decisions.
Establish a Strong Governance Structure
Governance structure defines roles, responsibilities, and decision-making authority for cybersecurity risk management. You need clear ownership at the board level, executive leadership, and operational teams.
Board oversight ensures cybersecurity risks receive appropriate attention alongside financial and operational risks. Directors should understand the organization’s risk appetite, major cyber threats, and effectiveness of implemented controls. Quarterly briefings keep boards informed without overwhelming them with technical details.
The Chief Information Security Officer (CISO) or equivalent executive owns the risk management program. This role reports to the CEO or Board rather than the CIO to maintain independence and appropriate organizational authority.
Risk committees review and approve risk treatment decisions that exceed delegated authority. Committee members represent business units, IT, legal, compliance, and finance to ensure balanced decision-making that considers all organizational perspectives.
Conduct Comprehensive Risk Assessments
Comprehensive assessments go beyond automated vulnerability scans to include manual testing, business impact analysis, and threat modeling. You examine risks from multiple angles to avoid blind spots that automated tools miss.
Red teaming simulates real adversary tactics to test detection and response capabilities. Unlike penetration testing that stops at initial compromise, red team exercises attempt to achieve specific objectives like data exfiltration or system destruction.
Business impact analysis identifies which systems and data matter most to operations. You interview process owners to understand dependencies, acceptable downtime, and recovery priorities. This information guides risk treatment decisions and disaster recovery planning.
Third-party assessments provide independent validation of your security posture. External auditors bring experience from multiple organizations and identify issues that internal teams might overlook due to familiarity with existing systems.
Implement a Layered Defense Strategy
Layered defense deploys multiple security controls so that if one fails, others still protect your assets. Attackers must defeat all layers to succeed, while defenders only need one layer to detect and block the attack.
Network segmentation isolates critical systems from general networks. You place high-value assets in separate network zones with strict access controls that prevent lateral movement if attackers compromise a user endpoint.
Zero trust architecture verifies every access request regardless of network location. Users and devices authenticate continuously, receiving minimum necessary permissions for each requested resource.
Endpoint detection response monitors devices for malicious activity, blocking threats that bypass perimeter defenses. Behavioral analysis identifies ransomware, credential theft, and command-and-control communications based on process behavior rather than known signatures.
Application security integrates security testing into the development lifecycle. Static analysis reviews source code for vulnerabilities before compilation, while dynamic analysis tests running applications for exploitable weaknesses.
Develop Incident Response and Recovery Plans
Incident response plans define procedures for detecting, containing, and recovering from security incidents. You document roles, communication protocols, escalation procedures, and recovery steps before incidents occur.
Playbooks provide step-by-step guidance for common incident types: ransomware, data breaches, DDoS attacks, and insider threats. Each playbook specifies who does what at each stage, preventing confusion during high-stress situations.
Regular testing validates that plans work as intended. Tabletop exercises walk teams through scenarios, identifying gaps in procedures or resources. Full-scale simulations test technical recovery processes and team coordination under realistic conditions.
Backup verification ensures you can actually restore from backups when needed. Test restorations confirm backup integrity and measure recovery time, so you know whether you can meet recovery objectives during real incidents.
Integrate Cybersecurity in the Supply Chain
Supply chain integration extends security requirements to vendors, service providers, and business partners. You assess third-party risks before onboarding and monitor continuously throughout the relationship.
Vendor security questionnaires collect information about security practices, certifications, and past incidents. You require evidence of controls like encryption, access management, and incident response capabilities.
Contractual obligations establish security requirements as legal commitments. Contracts specify data handling procedures, breach notification timelines, audit rights, and liability for security failures.
Continuous monitoring tracks vendor security posture through automated feeds of security ratings, breach notifications, and vulnerability disclosures. You receive alerts when vendors experience security incidents that could affect your organization.
Best Practices for Cybersecurity Risk Assessment
Risk assessment effectiveness depends on scope, methodology, and stakeholder engagement. You need accurate data, realistic scenarios, and buy-in from business leaders who must approve risk treatment decisions.
Build Cybersecurity into the Enterprise Risk Management Framework
Enterprise Risk Management (ERM) frameworks already exist in most organizations to manage financial, operational, and strategic risks. You integrate cybersecurity risks into existing ERM processes rather than creating parallel risk management systems.
Common risk language ensures cybersecurity risks are comparable to other business risks. You express cyber risks in terms that ERM committees understand: financial impact, operational disruption, reputational damage, and regulatory penalties.
Risk appetite statements define acceptable levels of cybersecurity risk just as they do for other risk categories. Boards articulate how much security risk the organization will accept to achieve business objectives, guiding risk treatment decisions.
Risk reporting consolidates cybersecurity metrics with other enterprise risks in board-level dashboards. Executives see cybersecurity alongside financial risks, competitive threats, and market changes, enabling informed resource allocation.
Identify Value-Creating Workflows
Value-creating workflows represent processes that directly contribute to revenue, customer satisfaction, or competitive advantage. You prioritize protecting these workflows because their disruption causes immediate business impact.
Process mapping documents how workflows function, which systems they depend on, and what data they consume or produce. Maps reveal critical dependencies that might not be obvious from system diagrams alone.
Failure scenarios model what happens if workflow components become unavailable. A payment processing workflow that depends on a third-party payment gateway fails if that gateway goes down, halting all revenue-generating transactions.
Protection priorities align security investments with business value. You spend more to protect revenue-generating systems than internal administrative tools because the business impact of their compromise is substantially higher.
Prioritize Cyber Risks
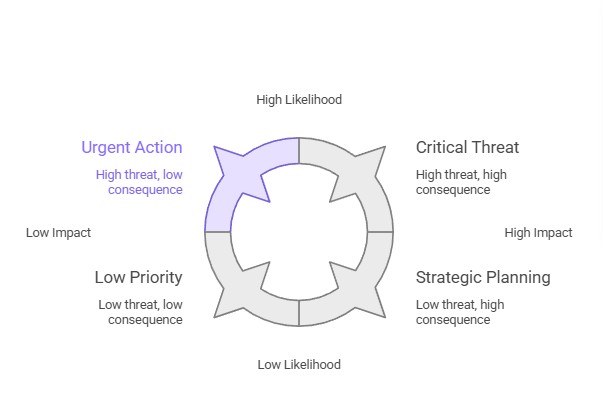
Risk prioritization ranks identified risks by combining likelihood and impact scores. You address high-likelihood, high-impact risks first, followed by risks that score high on one dimension but lower on the other.
Risk matrices visualize the risk landscape, plotting each risk on a 5×5 heat map with likelihood on one axis and financial/operational impact on the other. This visual prioritization ensures that “Low Likelihood, Extreme Impact” events (like a total database wipe) receive the same attention as frequent, smaller incidents. Clusters of high risks indicate where you should focus resources.
Risk scoring systems assign numerical values to facilitate comparison. Common approaches include multiplying likelihood and impact scores, or using the CVSS (Common Vulnerability Scoring System) for technical vulnerabilities.
Resource allocation decisions follow risk priorities. You invest in controls that reduce the highest-priority risks first, achieving maximum risk reduction per dollar spent.
Implement Ongoing Risk Assessments
Ongoing assessments incorporate risk management into daily operations rather than treating it as a periodic exercise. You continuously discover assets, identify vulnerabilities, and evaluate threats as your environment evolves.
Automated asset discovery maintains current inventories without manual effort. Tools scan networks and cloud environments to identify new devices, applications, and data stores as they appear.
Continuous vulnerability scanning tests systems for new weaknesses as vulnerabilities are disclosed. Scanners run daily or weekly rather than quarterly, reducing the window when unpatched vulnerabilities remain exploitable.
Threat intelligence integration updates risk assessments when new threats emerge. You receive feeds about active ransomware campaigns, zero-day vulnerabilities, and threat actor tactics, adjusting your security posture based on current threat landscape.
In Summary
Cybersecurity risk management protects your organization through systematic identification, evaluation, and treatment of security threats. The four-step process—identifying assets, analyzing risks, addressing vulnerabilities, and continuous monitoring—creates a cycle that adapts to evolving threats and changing business requirements.
Frameworks like NIST CSF, ISO 27001, and CIS Controls provide proven methodologies for implementing risk management programs. You select frameworks based on industry requirements, regulatory obligations, and organizational capabilities, customizing them to address your specific risk profile.
Strong governance structures, comprehensive risk assessments, layered defenses, and supply chain integration form the foundation of effective cyber risk management strategies. These elements work together to reduce your attack surface, improve incident response capabilities, and demonstrate due diligence to regulators and customers.
Organizations that invest in risk management reduce breach costs by 31%, achieve regulatory compliance more efficiently, and maintain operations during cyber attacks. You protect business value, customer trust, and competitive advantage through disciplined application of risk management principles.


